CCI has held, in virtual format, a meeting aimed at the Andalusian industry, presenting for the first time criminal prevention against technological crimes in industrial environments in accordance with compliance models.
The main objective of this meeting was to share experiences and lessons learned about cybersecurity in different sectors of the industry. During the meeting, a representative of the Andalusian Government presented the initiatives that are being developed, with special attention to aspects related to cybersecurity in the industry.
The CCI coordinator for Andalusia, Juan Miguel Pulpillo presented two documents developed by the CCI knowledge team “Good governance and Compliance”, group to which Juan belongs and which will be launched at the next International CCI Congress in September 2020

Juan M. Pulpillo emphasizes in Global Compliance, and the effort made by the CCI group to analyze all the elements that comprise it.
Corporate criminal responsibility is the set of policies, codes and culture of compliance that must be defined in any business and industrial corporation. Both individual legal responsibility and security must go hand in hand.
It also indicates with a use case about a technological crime the personal responsibility that it would suppose to us. Juan M. Pulpillo shows the infographic created by CCI as an awareness example for the entire industry and a very positive technique among the members of organizations.
All the industrial sectors are advancing in the digital transformation, and we have been able to learn how to integrate cybersecurity in the supply chain in this scenario, as well as the experiences in the incorporation of industrial cybersecurity by Phoenix Contact, OYLO and Entelgy Innotec Security , and how to achieve cyber resilience of industrial organizations in charge of Accenture Security.
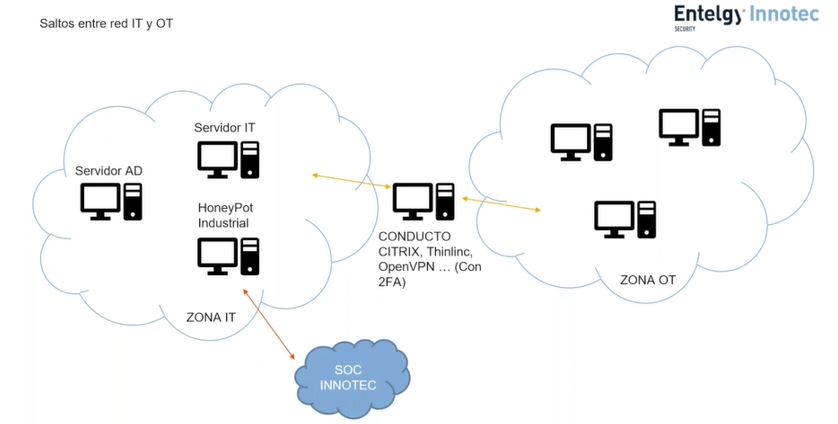
With a technical presentation, Francisco Ramírez, from Entely Innotec Security, explained the importance of separating the IT and OT fields and the threats found in industrial environments, the best known cases of different attacks on industrial control systems, the use of an industrial honeypot that allows us to analyze the types of attacks that our network is receiving, alert management and Threat Hunting.
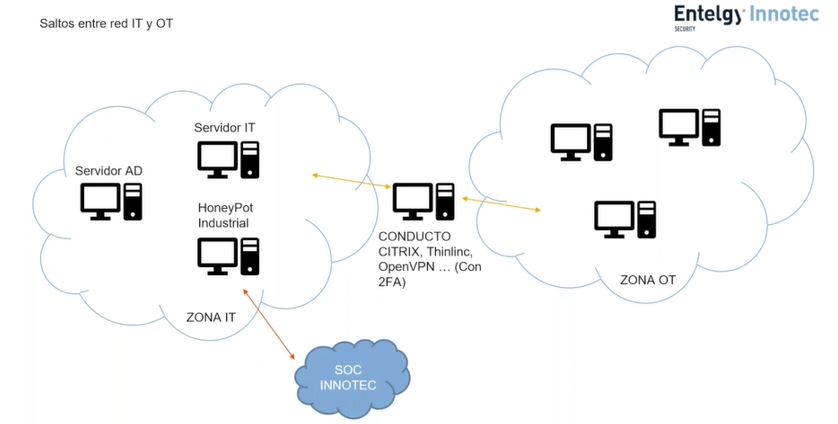
Also the creation of a gateway to the OT network, that is, the centralization of the connections of both environments.
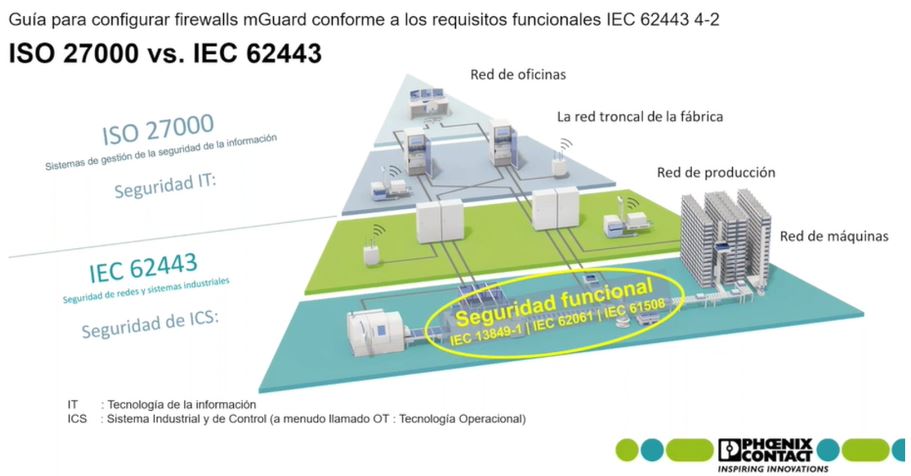
Next, the presentation of a guide to cover functional requirements according to the IEC42443 4-2 standard by Ramón Quirós, Phoenix Contact, mentions that there are more and more peopole concerned about cybersecurity and specifically the industrial sector, but it also demands a firm standard that talks about technological requirements.
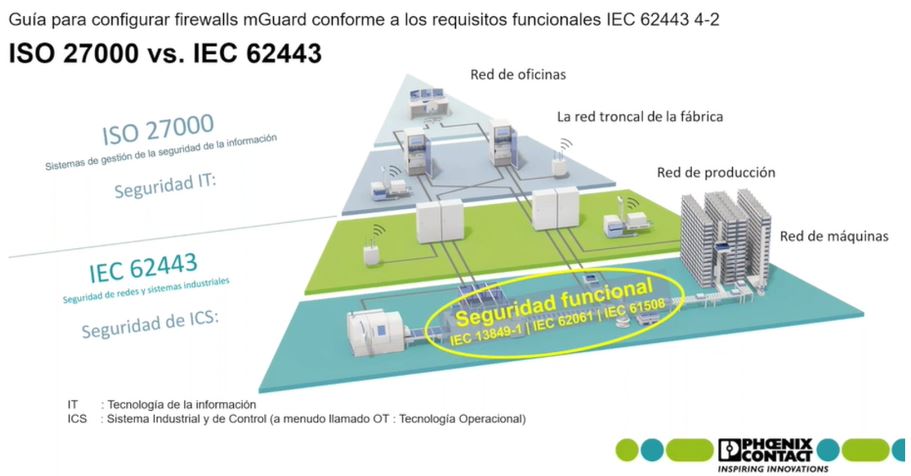
In OT environments, ICS security prioritizes equipment availability while in a corporate / IT environment, confidentiality prevails over integrity or availability. From Phoenix Contact they facilitate the task of interpreting and applying the IEC 62443 standard with the various guides available from their website.
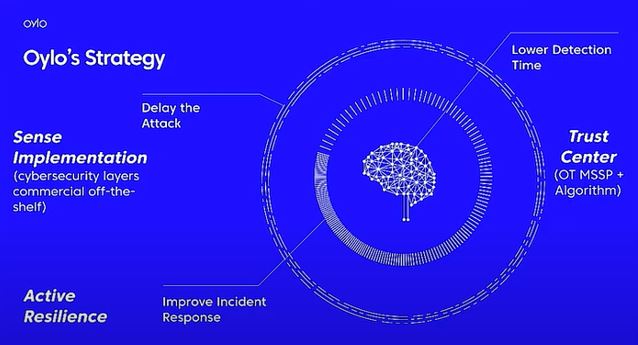
Eduardo Di Monte, Oylo Trust Engineering, put operational technology (OT) and the importance of certification in context.
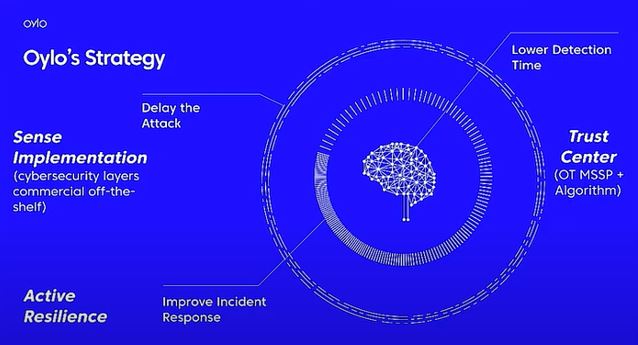
After several examples applicable in different industrial environments, Eduardo Di Monte talks about augmented reality, adapted technologies, and the different layers and their cybersecurity. The implementation of technologies with a good reputation, maturity, experiences and references is important since we are talking about critical infrastructures. The different architectural typologies of networks and other factors involved are also highlighted. It is not the same to speak about a single device or 140 that may be in an industrial plant. The design stage of the network architecture and analysis becomes decisive to subsequently make a correct deployment of the technology without having to invest in more devices to secure the network.
It highlights the importance of adding value to the business and not just think about cybersecurity.
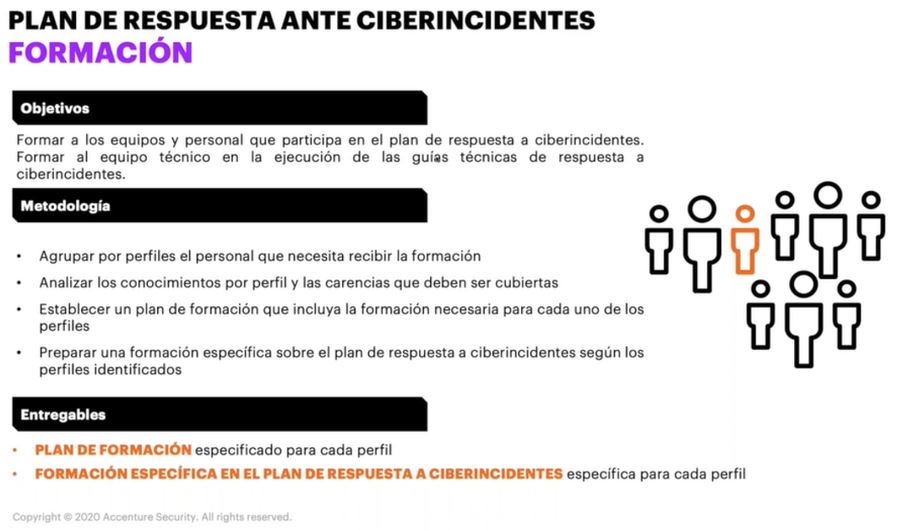
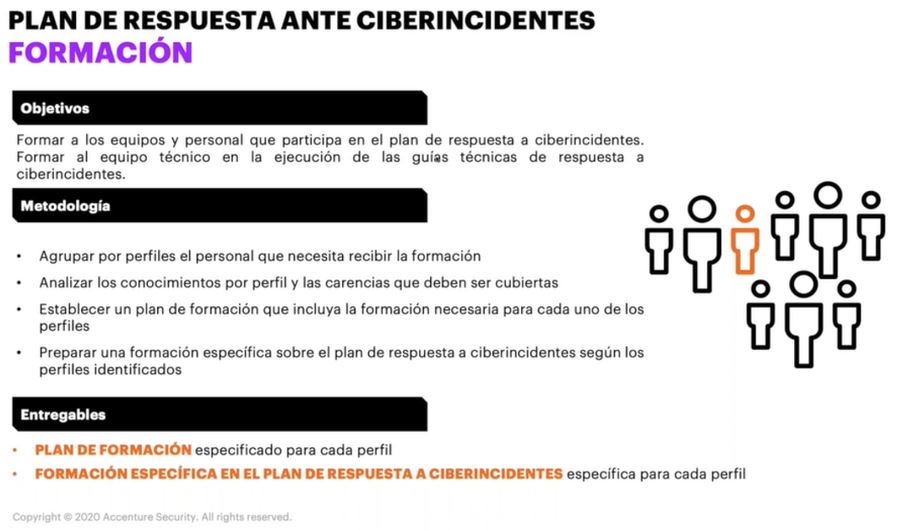
Lastly, and with regard to the papers from The Voice of the Andalusian Industry, David Marco, Accenture Security, talks about resilience, the importance of having a defined incident response plan.
The key to business is protecting assets, availability, and reputation. It is imminent to have to analyze the response plan of the organization on which you are going to work or, if there is not one, the realization of this. For this, a methodological approach must be given in which the flexible cyber incident response plan is carried out for each type of attack, the use of technical guidelines for cyber incident response (Containment, execution and recovery), the training of teams and personnel involved in the response plan, carrying out cyber exercises regularly and finally an evaluation of their results in order to correct errors in the procedures or the education and training of personnel.
INTERVIEWS
The meeting ended with interviews to managers of Andalusian industrial organizations who have shared valuable experiences and challenges to implement the protection of industrial infrastructure.
The three Andalusian professionals from different sectors (Oil & Gas, Electric and Water) answered the following questions:
What do you think could facilitate the incorporation of OT cybersecurity requirements in organizations in your sector?
What do you consider to be the most important difference between managing OT cybersecurity incidents and managing IT cybersecurity incidents in your sector?
Miguel Moreno, professional in the area of control systems, at Cepsa with more than 30 years of experience in various relevant companies in the sector, expresses the current need for top management support to facilitate the incorporation of OT cybersecurity requirements. He points out that these requirements must be provided according to the security level targets in each area and always with good technical and economic support behind. This together with a good awareness is a good basis for the subsequent management and evaluation of possible risks.
On the other hand, Miguel Moreno considers that the most important difference between managing OT cybersecurity incidents and managing cybersecurity incidents in IT environments in the petrochemical sector are the different levels within the crisis cabinet and including the professionals responsible for OT in such cabinet (previously this area was not involved) and inform the person in charge of communication, both internal and external.
On the other hand, Pablo Gómez-Calvente, a professional in cybersecurity in Smart Grid devices at ENEL, believes that it could facilitate the incorporation of OT cybersecurity requirements in organizations such as ENEL, the electricity sector, the inclusion of internal security policies, based on international standards or recommendations. from international organizations specialized in cybersecurity, NIS, ENISA or the CCI itself. Also the analysis of the technology that does not comply with the security requirements and subsequently evaluate the criticality of the devices to consider updating or changing them for ones that do comply. Today there are already manufacturers that meet several of the requested or mandatory standards within the organization.
For Pablo Gómez-Calvente, the most important difference is that OT incidents are more critical than those that may occur in an IT environment. Businesses can have much higher penalties.
Alfonso López-Escobar, head of cybersecurity at EMASESA with extensive experience in industrial automation, believes that there are not so many differences between sectors. He points out that the OT world is beginning to get very close to IT, and operational environments must be an important part to protect. Learning from external known cases are the easiest and safest in our own organization, the worst thing is that an incident happens to oneself and you have to learn by force.
In reference to critical infrastructures, Alfonso López-Escobar suggests that legal obligations have a great weight, which facilitates the incorporation of OT cybersecurity requirements in organizations. Cybersecurity must be tackled together and with effective communication between those involved. He also points out that the volumetry, the impact and the type of threat, especially if it is internal, are some of the differences to be highlighted between the management of OT and IT incidents.